Services
Discovery PhaseUX/UI DesignAI Development
Web Development
Mobile DevelopmentTest AutomationData EngineeringCloud Services
SalesforceSecurity
CTO-as-a-ServiceСlients
Case studies
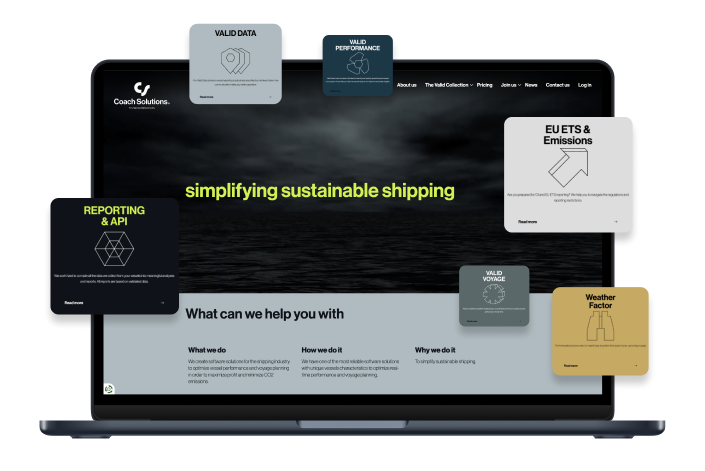
WendyAI-powered recruitment assistantBambooMicro-investment appCoin360Crypto exchange live data aggregatorEtergoSmart electric scootersCoach SolutionsWeb application penetration test
Industries
Knowledge base